With the recent releases of John the Ripper (1.7.8 and above) we now have password cracking with multiple cores available so we can crack SAP passwords faster than ever before. SAP password cracking requires the Community Edition otherwise known as the Jumbo Release to support the required hash formats.
Do not use this against systems you’re not authorised to do so.
Step 1: Dump the password hashes from SAP. You can use this ABAP Program to generate in the correct format for John the Ripper. You could alternatively dump these direct from your backend database but it needs to be in the format the code generates.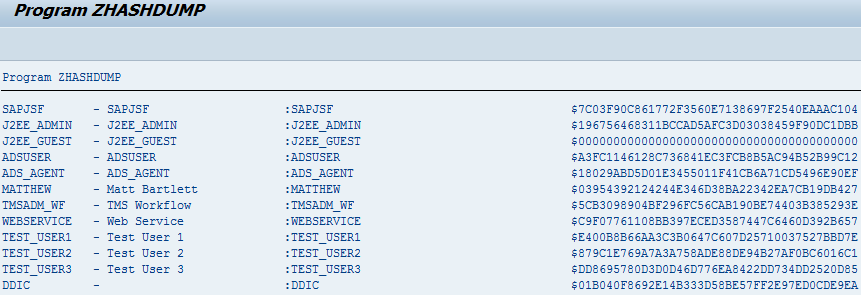
Step 2: Download and Install John the Ripper. In the video I optionally compile for my Linux Backtrack Server and enable OpenMP for multiple core processing as this is my preference but you could alternatively download a plain precompiled version. There are also Windows binaries available you can download complete with OpenMP enabled which is partially handy if you don’t have access to multiple platforms. Which ever version you download don’t forget you need the Jumbo Community Version.
Step 3: Simply run John the Ripper against the hashes this will run through its standard rules and attempt to brute force the passwords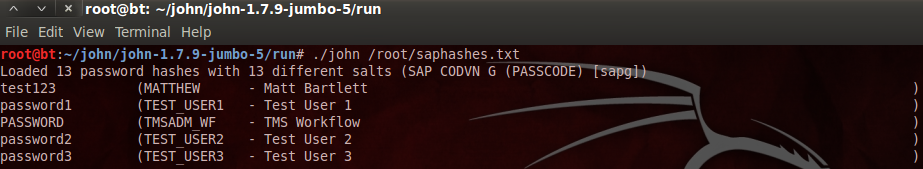 or with the –wordlist option to specify a dictionary attack based on any number of large word lists available.
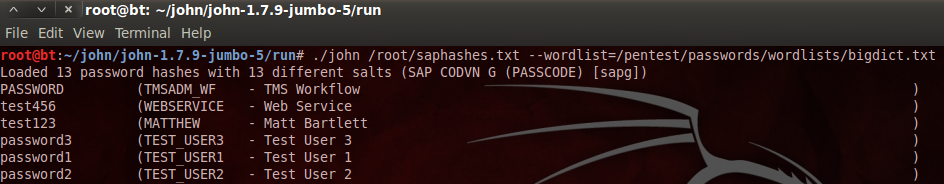
or with the –wordlist option to specify a dictionary attack based on any number of large word lists available.
SAP has a good note describing some features you can use to limit this type of attack – See SAP Note: 1237762
I can also recommend this book for much more information around this topic –
Hello matthew,
Can you tell me how to crack SAP password taken from SAPDIAG of Cain and Abel.
In your tutorial, your password appears to be in plain text while in our case, it does not appears in plain text.
Hi,
You must use the latest version of Cain and Abel
http://www.oxid.it/
Cain & Abel v4.9.43 released
– Added SAP R/3 sniffer filter for SAP GUI authentications and SAP DIAG protocol decompression.
You also notice you need to scroll the section that is the client decompressed part, in my example I’m about 25% down through the file.
Also did you know the same can be achived using wireshark and a plugin see – http://www.mattbartlett.co.uk/sap-password-sniffing-using-wireshark/
Thanks
Matt